A Complete Guide of BlueBorne Virus
Virus attack must not be strange to mobile phone users. Nowadays, there are thousands of viruses threaten the security of our portable devices. And among these viruses, BlueBorne virus would be the most common one. This virus affects not only our daily use of mobile phones but also our real lives. So, in order to help you better understand BlueBorne virus and keep your device away from this virus attack, we write this article to make a detailed introduction about it.
Part 1. What is BlueBorne Virus?
BlueBorne virus is vector that can attack our devices via Bluetooth. This virus can spread over the air and once it enters your phone, it will control the device completely. In addition, the Android models that it can corrupt are various, including Android, iOS devices, Windows and Linux. Therefore, if you don't take action to protect your phone, the device would have a big chance to be attacked by this virus, which could bring a big trouble to you.

Can't miss:
My Android Stuck on Boot Screen, How to Fix It?
iPhone Frozen During iOS Update, How to Fix It?
Part 2. How does BlueBorne Virus Work?
The attack of BlueBorne virus can be concluded as 3 stages:
Stage 1. Locate an active Bluetooth connection around it. Once you turn on the Bluetooth feature on your phone and connect it to Windows PC, Android Phone or iDevices, this virus can explore your device and locate it.
Stage 2. After locating a target device, the attacker is able to obtain the Mac address of the device which is an unique identifier of that device for network connections. Then the attacker will judge and confirm the operating system of the target device and begin to take complete control of it accordingly.
Stage 3. Next, the attacker will explore the weakness in the Bluetooth implementation on that operating system. Then it gains access to target device.
Part 3. Why is the Virus Dangerous?
Why we say this virus is dangerous? That because the conditions that can generate this virus is simple:
1. Active Bluetooth connection. To locate your device, this virus even does not need you to active pairing or discoverable mode, interact with other users, tap on any link or other operations.
2. The high compatibility of the virus. The BlueBorne attack is not limited to particular operating system or device. It can attack any device with Bluetooth feature.
3. Spread over the air. Unlike other virus, BlueBorne spreads through air rather than internet so it is more contagious.
4. Hard to be detected. This virus remains undetected and the traditional security methods cannot prevent the device from the airborne threat.
5. Take full control over your phone. It can access to all the components of the operating system, which means all the files on your device would be controlled by the attacker.
Part 4. Tips to Prevent Your Device from BlueBorne Virus Attack
It sounds that BlueBorne virus is horrible and difficult to be avoided. But we also can do some handful things to protect our mobile phones from the threat. The tips are listed below:
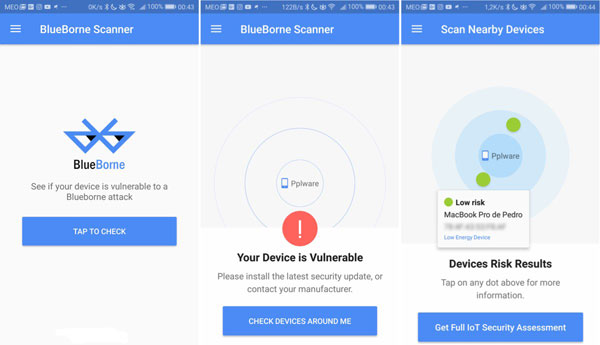
1. Use BlueBorne Vulnerability Scanner. To avoid BlueBorne virus attack, the first thing you should do is to check whether your device is endamaged by the attack or not. You can download and use BlueBorne Vulnerability Scanner app to help you. If you find that your device is vulnerable, you need to take actions to protect it.
2. Update the operating system of your device to the latest version. Check and update the system version regularly can help you avoid many problems.
3. Turn off Bluetooth when you needn't use it. As we have mentioned above, BlueBorne virus spreads over the air and Bluetooth. So you are advised to disable the Bluetooth feature when you do not need to use it. What's more, you can use other methods to transfer the files on your phone and reduce the operating frequency of Bluetooth.
4. Remove sensitive information or backup the data on your phone. To avoid virus attack, you are advised to delete all the sensitive information on your device and make a backup for the files on your device in case of data loss.
Related Articles:
Full Guide on How to Fix Android System Crash Issue
3 Methods to Resolve iPhone Stuck in Boot Loop
3 Solutions to Wipe Cache Partition on Android
Best Android File Transfer Alternatives for Mac [2021]

