How to Tell If Your Phone Has Been Cloned in 2023 [6 Alarming Signs]
The thought of someone gaining unauthorized access to our phones is a concern that crosses our minds from time to time. It's not uncommon to wonder, "Is my phone cloned?" This preoccupation stems from a growing awareness of the potential threats lurking in the digital realm.
Alright! Knowing how to tell if your phone has been cloned is a critical skill in safeguarding your privacy and personal data. Perhaps you've noticed strange activity on your device. Or maybe you've received texts or calls from unknown numbers. Well, this passage will explore the main telltale signs and discuss various methods to verify and fix the symptoms associated with phone cloning.
Part 1: What Is Phone Cloning
The transfer of data from one phone to another, including contacts, SMS, call logs, notes, recordings, calendars, photos, music, videos, documents, and applications, is known as phone cloning. This process is commonly utilized when a user wishes to move data from an old phone to a new one. There are various methods to clone a phone, such as utilizing third-party apps or software.
It is crucial to recognize that phone cloning can be utilized for nefarious purposes, such as stealing personal information or committing fraud. As a result, it is recommended that users only employ reliable apps and software when cloning their phones.

Click to Access:
- 6 Methods to Remotely Control iPhone 15/14/13/12/11/X/8/7 from Computer
- [Fixed!] How to Switch Android Phones without Losing A Thing?
Part 2: How to Get Your Phone Cloned
Most phones have SIM cards with protected IMEI numbers, but if someone can physically access the SIM card, they can copy its credentials for use on a blank SIM. Please note that some vulnerabilities exist as cloned phone symptoms, such as in the over-the-air carrier update protocol, allowing remote SIM cloning.
To prevent unauthorized access to your phone, avoid leaving it unattended and vulnerable to SIM card cloning. In crowded places, disable Bluetooth, Wi-Fi, and NFC to deter potential attackers who might use scanners to hijack your IMEI. (How to unlock the phone free with an IMEI number?) Additionally, consider using 3rd-party security apps that can help safeguard your phone and notify you of potential threats. Then, how to know/find out if your phone is cloned? We shall talk about this in the next section.
Note: Older CDMA phones (2G or 3G) on Sprint or US Cellular networks are at a slightly elevated risk of remote cloning, but such incidents are less common now due to improved security compared to the early days of mobile phone use.
Part 3: How to Tell If Your Phone Has Been Cloned
Tip 1. Find the calls or texts on your phone bill that you don't recognize
How to check/know if my phone is cloned? First, it is recommended to conduct a test by requesting friends and family to call your phone number. Additionally, an excessive amount of incoming calls and texts from unfamiliar numbers and senders may suggest that your phone and number have been compromised, resulting in a decrease in the number of calls and texts you typically receive.

Tip 2. Cannot receive calls and text messages
If you stop receiving texts or calls and encounter issues like No SIM card errors or mobile data problems, someone might have cloned your phone. This is a direct proof for how to tell if your phone is cloned. Contact your service provider immediately; you may need a new SIM card due to a potential phone cloning issue.
Tip 3. Receive a text message asking you to restart your phone
Be cautious of unexpected requests to power off or restart your phone, as phone cloners may require a brief window of time to establish their own replicated devices. It is advisable to verify that such requests are coming from a legitimate service center before complying, as restarting one's phone is a typical method of resolving technical issues. In severe cases, it may be necessary to terminate your account and obtain a new phone number.

Can opening spam messages result in a cloned phone? This isn't a telltale sign for how to know if someone cloned my phone, but they might contain harmful attachments that can introduce malware, leading to potential issues like phone cloning. Phone cloning involves duplicating data from one device to another, often used for data transfer.
Tip 4. Your phone displays the wrong location on Find My Phone/Device
How do I know if my phone has been cloned when none of the characteristics above exhibit? Use location-tracking apps like Find My iPhone (Apple) or Find My Phone (Android). (How to turn off Find My iPhone remotely?) These apps, including Life360, Android Device Manager, and Find My Mobile (Samsung), display your device's location. If your IMEI or EID number has been cloned, you'll notice multiple locations.

Tip 5. You're locked out of your accounts unexpectedly
Attackers may hijack SIM cards using stolen phone numbers. Once they control your phone service, they can reset passwords and access accounts associated with your login name. How can you tell if your phone has been cloned? Contact your cellular provider to block the cloned device, as each handset has a unique radio fingerprint that sets it apart from the original serial number assigned to you.
Tip 6. Your carrier prompts you that your SIM has been updated
How do you know if your phone is cloned via SIM card? OK, if the fraudster has successfully activated the cloned SIM of your phone number, a message will be received from your phone carrier indicating that your SIM has been updated. (Can you activate an iPhone without SIM?) This serves as a verified indication that your phone has been cloned. Likewise, it is advised to contact your phone carrier's customer care immediately and proceed with the necessary actions.

Further Reading:
- How to Clone/Duplicate SIM Card? [4 Options Few People Know]
- How to Erase Deleted Files on iPhone Permanently
Part 4: What If You Know Your Phone Has Been Cloned
Phone cloning can have serious consequences, but taking prompt and effective action can help mitigate potential damage and secure your personal information. To rectify the consequences of phone cloning, you can proceed with these actions:
- Change important passwords, but avoid using the cloned phone.
- Check your bills for unauthorized charges.
- Disable SMS logins and use app-based two-factor authentication.
- Consider a factory reset to remove potential malware.
- Contact your mobile carrier to report the issue and get a new number.
- Protect your phone's unique identifiers and avoid sharing them recklessly.
Bonus: How to Clone Your Phone to a New Phone Securely
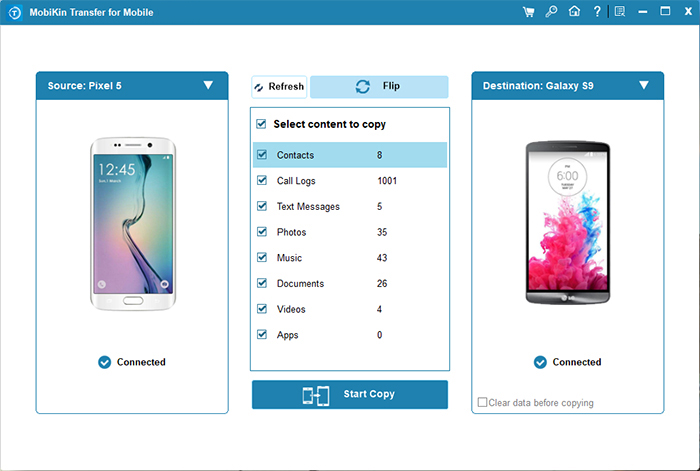
Has my phone been cloned? If not, and you are wondering how to make it, you may consider using 3rd-party software to clone your mobile content, particularly after upgrading your phone. MobiKin Transfer for Mobile (Windows & Mac) is more reliable than official tools and offers the advantage of selecting the specific content you wish to clone, regardless of the operating system your phone utilizes. By cloning your phone for personal use, you can alleviate concerns about privacy and the potential leakage of account information.
Main features of MobiKin Transfer for Mobile:
- Clone your phone quickly while maintaining data error-free.
- Copy files across various device combinations: Android to Android, Android to iPhone, iPhone to iPhone, and iPhone to Android.
- Seamlessly transfer various file types, including contacts, SMS, music, videos, photos, call logs, documents, apps, and more.
- Compatible with a broad spectrum of Android/iOS devices, including Samsung, Huawei, Sony, Xiaomi, OPPO, Google, HTC, LG, Motorola, iPhone 15/14/13/12/11/X/8/7, and more.
- It won't invade your privacy.
How to clone your phone with MobiKin Transfer for Mobile?
- To get started, open the program on your computer, making sure it's downloaded and installed.
- Connect both devices to your computer using USB cables.
- Then, follow the directions on the screen to recognize both devices.
- If you accidentally swapped the source and destination devices, just click the "Flip" button to correct their positions.
- Once you've completed the initial setup, select the data types you want to transfer and click the "Start Copy" button.
Roundup
This article has delved into the realm of phone cloning and how to tell if someone cloned your phone, shedding light on the common signs associated with this invasive practice. Beyond that, we explored the importance of safeguarding your personal information from prying eyes.
As technology continues to evolve, staying informed and vigilant is crucial. By recognizing the red flags of device cloning and understanding the methods to verify these symptoms, you can take proactive measures to protect your digital privacy like a pro.
Related Articles:
How to Transfer Data from Android to iPhone after Setup? 8 Techniques 2024
How to Stop Your Employer from Tracking Your Phone (Android & iPhone)
How to Fake Location on Find My iPhone? 6 Methods Most People Don't Know.
Huawei Phone Clone Troubleshooting: Scenes, Solutions & an Alternative



